5 June 2018
Post-Quantum Cryptography
cyber security in the age of quantum computing
We make daily use of electronic devices
that communicate information over the internet: smartphones, tablets, computers and soon the ‘internet of things’. Of these devices 90% regularly collect personal information from the cloud, like health- or bank data, addresses, usernames, passwords and pictures. In order to secure these personal data, modern communication channels use cryptographic security measures that hide it from unwanted third parties. Lots of these encryption techniques rely on solving complicated mathematical problems, so that someone willing to crack the code would require an unreasonable amount of computational resources. Yet, already in 1994 mathematician Peter Shor identified a theoretical threat to most of modern encryption technologies. He was able to show that an efficient algorithm exists to solve these mathematical puzzles exploiting the strange parallel computations of so called ‘quantum computers’. For a long time these machines, harnessing the weirdness of quantum mechanics, have only been theoretical constructs in the minds of scientists - but more recently small start-ups and big tech companies alike have come to acknowledge the realisability of true quantum computations in the foreseeable future. And one of the most apparent consequences of this event will be the compromise of our data encryption. Therefore, discussions of possible solutions to this outlook are of critical importance.
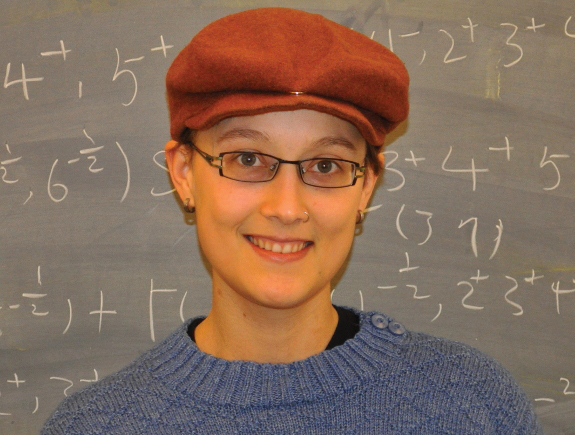
On June 5th in the Science Café Nijmegen, mathematician and cryptography scientist Simona Samardjiska (Radboud University) will discuss (in English) the topic of post-quantum cryptography. Simona will bring you up to speed about quantum computing and the basics of cryptography. Building on this she will illustrate how quantum computing can affect and even undermine traditional cryptography, thereby compromising much of the security infrastructure we use in our daily life. However, not all hope is lost! She will gracefully provide a walk through her theoretical research on post-quantum cryptography and its potential to mitigate the emerging deficiencies, introduced by quantum computing.



 Attend
Attend